Ghost Security Skills/Plugin Marketplace
Plugin marketplace repository for Ghost Security's AI-native application security skills for Claude Code.
Quick Installation
With Claude Code:
claude plugin marketplace add ghostsecurity/skills
claude plugin install ghost@ghost-security
claude
Alternatively, install the skills plugin within Claude Code:
/plugin marketplace add ghostsecurity/skills
/plugin install ghost@ghost-security
Currently, you will need to restart Claude Code for the plugin to load.
Comprehensive Documentation
Full documentation, tutorials, and video guides at ghostsecurity.ai.
Skills in this Repository Marketplace
| Skill | Description |
|---|---|
ghost-repo-context | Build shared repository context (business criticality, sensitive data, component map) |
ghost-scan-deps | Exploitability analysis of dependency vulnerabilities (SCA) |
ghost-scan-secrets | Context assessment of detected secrets and credentials |
ghost-scan-code | AI-powered detection of code security issues (SAST) |
ghost-report | Combined security report across all scan results |
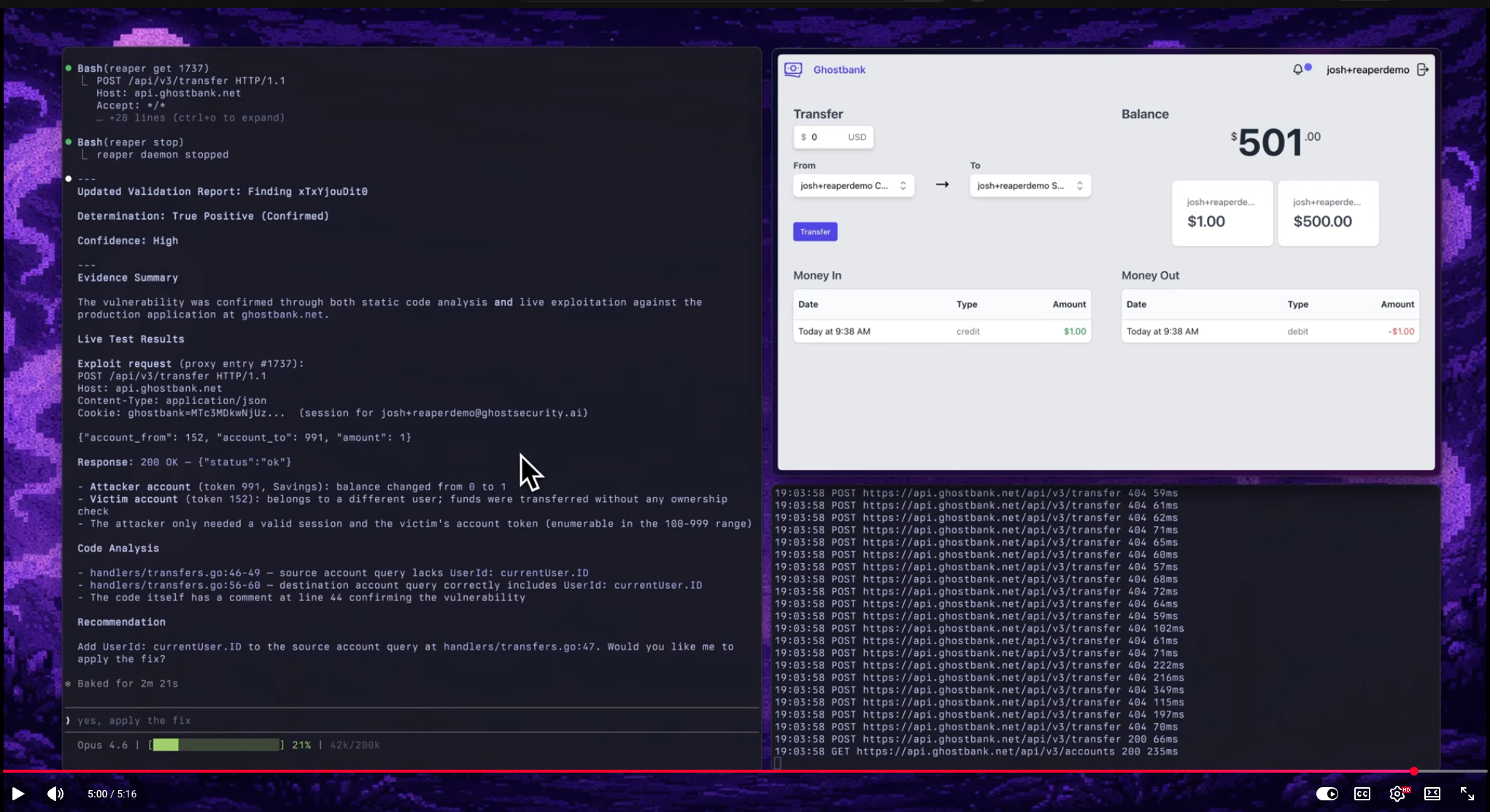
ghost-validate | Dynamic validation of findings against a live application (DAST) |
ghost-proxy | HTTP proxy for the ghost-validate skill |
ghost-repo-context
ghost-scan-code
ghost-scan-deps
ghost-scan-secrets
ghost-validate
ghost-report
Contributions, Feedback, Feature Requests, and Issues
Open an Issue per the Contributing guidelines and Code of Conduct
License
This repository is licensed under the Apache License 2.0. See LICENSE for details.